DB FPX 9803 Assessment 3
Free Download
DB FPX 9803 Assessment 3 Project Results Data Collection and Analysis
Student Name
Capella University
DB-FPX9803 Project Results
Professor Name
Submission Date
Table 1. Participant Demographics
Participant | Title | Industry | Retail experience (years) | Leadership experience (years) | Region |
P1 | Manager | Online fashion | 3+ | 3+ | U.S. |
P2 | Manager | Online fashion/retail | 3+ | 3+ | U.S. |
P3 | Manager (unnamed) | Online fashion | 3+ | 3+ | U.S. |
P4 | Manager (unnamed) | Online fashion | 3+ | 3+ | U.S. |
P5 | Mid-level manager | Online fashion/retail | 3+ | 3+ | U.S. |
P6 | Quality assurance manager | Online retail (health, beauty, electronics) | 3+ | 3+ | U.S. |
P7 | Manager (compliance & anti-counterfeit) | Online retail (fashion, consumer goods) | 3+ | 3+ | U.S. |
P8 | Founder | E-commerce (electronics, lifestyle) | 3+ | 3+ | U.S. |
P9 | Manager | Online retail (fashion, consumer goods) | 3+ | 3+ | U.S. |
P10 | Operations manager | Online retail (electronics, health, fashion) | 3+ | 3+ | U.S. |
P11 | Founder/manager | Online retail (multiple industries) | 3+ | 3+ | U.S. |
Note. Table 1 shows participant demographics for each interview.
Table 2. Participant Interview Overview
ID | Duration (Approx.) | Eligibility | Inclusion/Exclusion for Coding |
P1 | ~15 minutes | Meets all criteria | Not Included Lack depth, narrative rigor. The point of saturation happened after interview P9. Thematic coding was entirely performed with the help of nine transcripts (P3-P11) but P1 and P2 were to be utilized in procedural documentation. |
P2 | ~13 minutes | Meets all criteria | Not Included Are not so rigorous in either depth or narrative. At the interview P9, the information saturation was attained. Nine transcripts (P3 -P11) and 1 and 2 were fully coded thematically and stored to serve as procedural documentation. |
P3 | ~11 minutes | Meets all criteria (Manager, 3+ years, Anti-CF exp.) | Included – Full responses relevant |
P4 | ~10 minutes | Meets all criteria | Included – Sufficient relevant content |
P5 | ~12 minutes | Meets all criteria | Included – Detailed operational info |
P6 | ~16 minutes | Meets all criteria | Included – Rich technical data |
P7 | ~13 minutes | Meets all criteria | Included – Strong thematic alignment |
P8 | ~13 minutes | Meets all criteria (Founder, Cybersecurity background) | Included – High relevance |
P9 | ~13 minutes | Meets all criteria | Included – Complete, usable interview |
P10 | ~15 minutes | Meets all criteria | Included – Extensive insight provided |
P11 | ~13 minutes | Meets all criteria (5+ years, Founder) | Included – Thematic relevance confirmed |
Note. Table 2 represents the participant interview overview.
Table 3. Initial Code Development and Refinement
Section | Code category | Initial Code | Definition | Supporting Quote | Final refined code |
Technological challenges | Detection limitations | Difficulty in identifying counterfeits | Challenges in detecting counterfeit goods using existing tech or manual means. | “Even though we have strong controls, it’s impossible to check every single product and seller…” (P11) | Technological limitations in detection |
Technological challenges | Integration issues | Difficulty integrating new tools | Complications arise from implementing or aligning new technology with existing systems. | “Sometimes, you know, it takes time to integrate these new tools and systems into our operations fully.” (P11) | System integration constraints |
Impact on revenue | Lost sales & conversions | Revenue loss due to counterfeits | Financial impact on sales and conversion rates caused by counterfeits. | “It probably costs us about 25% of our conversions… a couple million.” (P3) | Sales revenue loss |
Impact on revenue | Customer churn | Losing repeat customers due to distrust | Counterfeit experiences reduce customer trust and repeat buying behavior. | “Customers who have encountered counterfeit issues are 72% less likely to return for additional purchases.” (P7) | Customer retention decline |
Regulatory approaches | Legal compliance gaps | Weak or unclear regulations | Lack of sufficient legal frameworks or enforcement to support anti-counterfeit efforts. | “Clearer legal provisions and stronger enforcement of law… are essential.” (P9) | Regulatory enforcement needs |
Regulatory approaches | Collaborative frameworks | Need for shared industry standards | Importance of cross-platform regulatory collaboration and data sharing. | “A shared database updated in real time across major e-commerce platforms… would serve as an early warning system.” (P10) | Industry-wide collaboration imperative |
Note. Table 3 shows the initial code development and refinement of the project.
Table 4. Categories and Aligned Codes
Section | Category | Definition | Contributing refined code | Supporting Pattern Evidence |
Technological challenges | Detection limitations | Limitations in accurately identifying counterfeit goods using current systems. | – Technological limitations in detection | Participants reported difficulty verifying authenticity due to sophisticated counterfeit packaging (P6, P8, P11). |
Technological challenges | Integration issues | Barriers to effectively implementing new technological systems. | – System integration constraints | Mention of delays and operational disruptions during tool adoption or system syncing (P6, P10, P11). |
Impact on revenue | Lost sales & conversions | Revenue loss due to customers unknowingly buying counterfeit goods or leaving the platform. | – Sales revenue loss | Direct losses are estimated in millions due to lost conversions (P3, P10). |
Impact on revenue | Customer churn | Customers stop buying after encountering a counterfeit due to broken trust. | – Customer retention decline | Patterns of decreased repeat purchases and lower post-purchase engagement (P7, P9, P11). |
Regulatory approaches | Legal compliance gaps | Inadequate laws or enforcement to deter counterfeit distribution. | – Regulatory enforcement needs | Calls for clearer rules and more support from legal frameworks (P9, P10). |
Regulatory approaches | Collaborative frameworks | Necessity for shared standards and cooperation across companies/platforms. | – Industry-wide collaboration is imperative | Emphasis on shared databases and joint enforcement practices (P10, P6). |
Note. Table 4 shows how categories are aligned with the codes.
Table 5. Themes from Analysis
Theme | Participant quote | Definition |
Technological challenges and solutions in combating counterfeit products to protect revenue | “Fake electronics are so good now that just looking at them isn’t enough… we had to add automation and better detection tools.” – P8. | Such theme means the shortcomings of the conventional means to detect fake products and the shift to the new sophisticated technologies in order to preserve the authenticity and efficiency of functioning. |
“We use AI-powered systems to detect and flag unusual inventory behaviors that may indicate counterfeit activities.” – P6. | To beat the advanced level of counterfeit, companies adopt multi-layered technologies such as AI, QR codes, and digital verification tools to defend the brand image. | |
Impact of counterfeit products on revenue and market share | “It probably costs us about 25% of our conversions… a couple million.” – P3 | This theme is a first hand manifestation to the actual financial implications of fake products, such as revenue and market share loss and customer trust and loyalty. |
“Customers who have encountered counterfeit issues are 72% less likely to return for additional purchases.” – P7. | The incidents of counterfeit result into customer loss, decreased repeat business and brand equity damage which affect the long term revenue streams. | |
Regulatory and collaborative approaches to counterfeiting prevention and revenue protection | “Clearer legal provisions and stronger enforcement of law… are essential.” – P9. | The theme also emphasizes the necessity to intervene by the government, create more powerful legal structures, and uniform regulations that will allow fighting against counterfeit operations successfully. |
“A shared database updated in real time across major e-commerce platforms… would serve as an early warning system.” – P10. | The cooperation of companies, platforms, and regulators is viewed to be crucial in avoiding the entrance of fake products and helping to maintain the protection of revenues. |
Note. Table 5 shows all the themes with their definitions from the analysis.
Table 6. Theme 1: Technological Challenges and Solutions in Combating Counterfeit Products to Protect Revenue
Conceptual pattern | Core codes | Pattern evidence | TPB Domain |
Limitations of traditional methods | – Technological limitations in detection | “Fake electronics are so good now that just looking at them isn’t enough…” – P8. “They replicate packaging with high accuracy…” – P6. | Attitude toward behavior |
Adoption of advanced technologies | – AI-powered detection systems – authentication tags & QR codes | “We use AI-powered systems to detect and flag unusual inventory behaviors…” – P6 “Serialization and authentication technology are used…” – P10 | Perceived behavioral control |
Operational efficiency through automation | – System integration constraints – improved verification speed | “We added automation… now our support team spends less time on counterfeit issues.” – P8 “QA inspection time cut by nearly 50%.” – P6 | Perceived behavioral control |
Stage-wise tech intervention | – Multi-stage anti-counterfeit checks | “We validate product QR codes and packaging inconsistencies at the warehouse stage.” – P6 “Digital verification before listing.” – P8. | Attitude toward behavior |
Challenges in tech integration | – Integration and onboarding delays | “Initially, it slowed things down… onboarding took longer.” – P10 | Perceived behavioral control |
Note. Table 6 shows theme one and how this aligns with the TBP framework, with the codes.
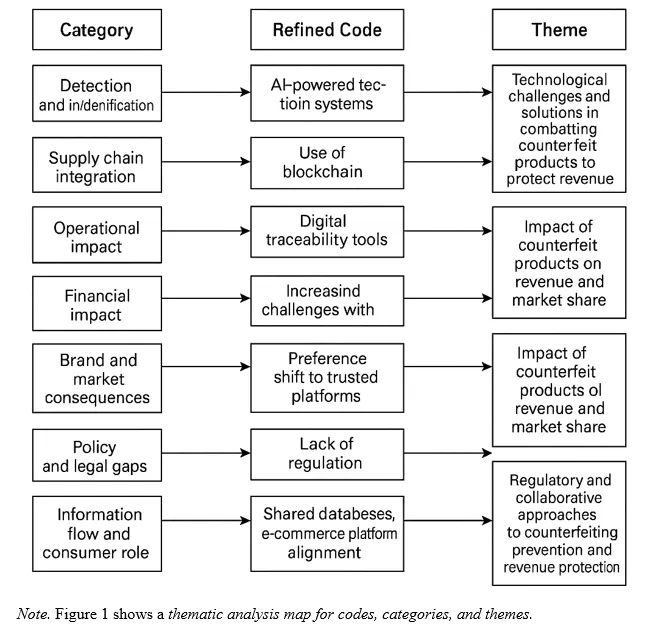
Theme 1 will be dealing with the technological approach and operational modifications that organizations make to counterfeit product fight, and that is directly connected to the attitudinal domain of the TPB framework. The stated discontent toward the conventional forms of detection (i.e. visual inspection or manual vetting of packaging) shows the negative disposition towards the old-fashioned practices. It is in line with perceived behavioral control to introduce and use AI-driven detection systems, QR codes, and automation.
When the companies report shorter inspection time and faster recognition of counterfeit, which builds up the conviction that they can implement the change, that, based on TPB, reinforces the intention to sustain or grow these behaviors. The theme in discussion also concerns the dilemma between technological potential and challenges faced during integrating the technology, which gives a more accurate perspective on the dilemma of behavioral control in reality. Despite the effectiveness of the systems, the delays of integration and the complexity of the process of onboarding emphasize the control limits and can influence the behavior of implementation.
Table 7. Theme 2: Impact of Counterfeit Products on Revenue and Market Share
Conceptual pattern | Core codes | Pattern evidence | TPB Domain |
Loss of sales and conversions | – Sales revenue loss | “It probably costs us about 25% of our conversions… a couple million.” – P3. | Attitude toward behavior |
Customer distrust and churn | – Customer retention decline | “Customers who have encountered counterfeit issues are 72% less likely to return for additional purchases.” – P7. | Subjective norm |
Negative brand perception | – Damaged brand image | “If you get a reputation for selling fake products… It’s a major blow.” – P5. | Subjective norm |
Operational resource strain | – Increased complaints and returns | “The number of returns due to fake suspicions has reduced… which used to consume time and cash.” – P9. | Attitude toward behavior |
Decline in market share | – Competitive disadvantage | “These fakes hurt not just sales but also how people see our brand compared to others.” – Implied in multiple accounts (P3, P6, P10) | Subjective norm |
Note. Table 7 shows theme two and how this aligns with the TBP framework, with the codes.
The second theme reveals the immense change of attitudes of managers who are directly affected by the losses in money as a result of fake products. According to the TPB, any kind of undesirable responses will be supported by negative outcomes, which in turn will trigger further aggressive anti-counterfeit measures following the revenue protection objectives. Subjective norms fall under distrust and negative brand perception by customers which are the influence of the expectations of others on the intention of a person.
Equipment failure to attract or keep returning customers once they experience the counterfeit experience or when the brand equity suffers in the marketplace, social pressure among the stakeholders, consumers and partners builds up. Strain in operations that is manifested in the use of resources in dealing with complaints that are resource-demanding strengthens the attitude towards investing in preventive mechanisms. This intensifies the behavioral intention to act which TPB holds to be strongest when all three domains, attitude, norms and control are activated.
Table 8. Theme 3: Regulatory and Collaborative Approaches to Counterfeiting Prevention and Revenue Protection
Conceptual pattern | Core codes | Pattern evidence | TPB Domain |
Need for stronger legal frameworks | – Regulatory enforcement needs | “Clearer legal provisions and stronger enforcement of law… are essential.” – P9. | Subjective norm |
Lack of uniform industry standards | – Inconsistent compliance practices | “Different sellers follow different rules, and it creates gaps that counterfeiters exploit.” – Implied across participants (P6, P7, P9) | Subjective norm |
Importance of cross-sector collaboration | – Industry-wide collaboration is imperative | “A shared database updated in real time across major e-commerce platforms… would serve as an early warning system.” – P10. | Perceived behavioral control |
Information sharing and transparency | – Platform integration for authentication | “We stay in touch with the brands… and update each other on how to spot fake products.” – P11. | Perceived behavioral control |
Consumer education support from policy | – Public awareness initiatives | “Educating customers on spotting fakes is essential, but it needs broader backing.” – P3, P4 (customer education tied to broader systemic support) | Attitude toward behavior |
Note. Table 6 shows theme three and how this aligns with the TBP framework, with the codes.
Theme 3 explains the role of subjective norms in managerial behaviour based on industry expectations and regulation of behaviour. The participants seem to be in need of a more solid legal framework and the standardization of sellers. The TPB suggests that the managers who believe that they are exposed to stricter compliance in the areas of norm (legal or social), the higher they tend to conform their actions within that industry structure, not only to safeguard revenues but also to preserve a good reputation. The cross-sector and integration of platforms are operational avenues that can lead to organizations improving their perceived behavioral control.
Figure 1. Thematic Analysis Map
Instructions to write
DB FPX 9803 Assessment 3
Instruction file for DB FPX 9803 Assessment 3 will be added soon.
References for
DB FPX 9803 Assessment 3
References will be added soon.
Capella Professor to choose for
DB FPX 9803 Assessment 3
- Bradly Roh.
- Melvia Scott.
- Jo‑Rene Queensberry.
- Paul Tovbin.
- Andrew Borchers.
(FAQ's) related to
DB FPX 9803 Assessment 3
Question 1: Where can I get a free sample for DB FPX 9803 Assessment 3?
Answer 1: Get a free sample for DB FPX 9803 Assessment 3 from the dbfpx.com.
Do you need a tutor to help with this paper for you within 24 hours
- 0% Plagiarised
- 0% AI
- Distinguish grades guarantee
- 24 hour delivery
Next Assessment: