DB FPX 8840 Assessment 2
Free Download
LEVERAGING MACHINE LEARNING ALGORITHMS to LOWER FRAUDULENT ACTIVITIES
By
Student name
DB-FPX8840 Seminar: General Management Topic Development
Professor Name
Submission Date
Insert the correct Dean’s name and credentials.
School of _____
A Capstone Work Presented in Partial Fulfillment
Of the Requirements for the Degree
Insert correct degree designation
Capella University
Month & year of dean’s approval
© Learner name, year
Abstract
The aim of the abstract is to present an accurate and brief summary of the important aspects of your capstone project. Prepare the abstract in the form of a lump-sum paragraph with no first-line indent. Discuss the following areas (not more than 400 words). Summary of Research topic (1-5 sentences): a summary of your capstone research topic. State the justification of your research and why the research the capstone deals with is necessary.
Cite your research questions, including the same words that you used in your capstone sections. Method of the research (1-2 sentences). Overview of the research process employed in the study. Population and sample (1- 2 sentences). Talk about the population and sample, with high-level demographic data about your participants. In case it was secondary data, explain the data set. Data analysis (1-2 sentences): A summary of your data analysis. Findings (1-3 sentences): A summary of your research findings and conclusion(s). Explain the practical implications of your project and deliverables that you produced.
Recommendations on writing a good abstract. (a) The abstract can be considered representative of your work. Your abstract will be examined to enable the researcher to decide whether your article is worth reading and to consider it in relation to their literature review. Your field colleagues will read your abstract so that they can understand more about the nature and quality of your doctoral work.
Therefore, the abstract is a documentation of your level of doctoral work. (b) Appendix: further specifications to write an abstract are in sections 3.3 of the APA Publication Manual, 7th edition, or at Campus at Academic Writer, https://academicwriter-apa-org.library.capella.edu/learn/browse/QG-59?group=All&view=list&term=abstract&sort=asc (c) References are generally not used in the abstract, as the focus is on the study, the research, and the findings.
FParagraph and Page Formatting for the Abstract. Prepare the abstract in a single block (in one paragraph) (do not indent the first line) and use one-half space between sentences. Left hand flush, ragged right. No justification of the right margin. Headings, bullets, and bold should not be used. The Abstract page is not numbered, and the word Abstract is not present in the Table of Contents.
Dedication
This dedication page is optional. It is your acknowledgment, indicating your appreciation and respect for significant individuals in your life. The dedication is personal; thus, any individuals named are frequently unrelated to the topic of the capstone.
Typically, learners dedicate the work to the one or two individuals who instilled the value of education and the drive to succeed in educational pursuits. Learners often dedicate capstones to relatives, immediate family, or significant individuals who have supported them or played a role in their lives.
Avoid identifying participants or anyone connected with the research site. You may use individuals’ titles with no name (e.g., “Thanks to the research director and site proctor for their help”). Or you may name individuals without connecting them to the site (e.g., “Thanks to Abdul Ibrahim and Mary Carson for their help”). Typically, avoid naming the site.
Note: if the Abstract runs onto a second page, change the page number of the Dedication to 4.
Acknowledgments
This recognition page is not compulsory. The acknowledgements do not act like the dedication in that they consider people who helped with your academic work, as about the advanced doctoral manuscript, or who served in your academic career, as it pertains to the research of the advanced doctoral manuscript. This could imply a mentor and a committee member, advisor, online or colloquia faculty, and other support individuals at Capella or other organizations. In case you were supported by fellowships, grants, or other organizational assistance, you should state it in this section. The credit is also suitable to give credit to statisticians, transcriptions, permission to use an instrument, and the like.
Do not name the participants or anybody related to the research site. You can also use the name of individuals with no title (e.g., thanks to the research director and site proctor, their assistance). Or you can call people without relating them to the site (e.g., “Thanks to Abdul Ibrahim and Mary Carson for helping them out). Generally, you should not give the name of the site. The learners tend to appreciate whoever has granted them the right to use an instrument.
Table of Contents
Acknowledgments………………………………………………………………………………………………… 4
List of Tables……………………………………………………………………………………………………….. 7
List of Figures……………………………………………………………………………………………………… 8
SECTION 1. PROJECT DESCRIPTION……………………………………………………………….. 9
Overview of the Project………………………………………………………………………………………… 9
Problem Statement and Purpose……………………………………………………………………………… 9
Theoretical Framework………………………………………………………………………………………….. 9
Project Context…………………………………………………………………………………………………….. 9
Historical Background and Current Trends……………………………………………………………. 9
Synthesis of the Scholarly Literature…………………………………………………………………….. 9
Synthesis of the Practitioner Literature………………………………………………………………….. 9
Alignment of the Project With the Literature and Discipline……………………………………. 9
SECTION 2. PROCESS……………………………………………………………………………………… 10
Project Questions………………………………………………………………………………………………… 10
Project Design/Method………………………………………………………………………………………… 10
Stakeholders, Participants, and Target Audience…………………………………………………….. 10
Role of the Researcher………………………………………………………………………………………… 10
Project Study Protocol………………………………………………………………………………………… 10
Sample…………………………………………………………………………………………………………….. 10
Data Collection………………………………………………………………………………………………… 10
Ethical Considerations…………………………………………………………………………………………. 10
Data Analysis…………………………………………………………………………………………………….. 10
SECTION 3. FINDINGS AND APPLICATION………………………………………………….. 12
Relevant Outcomes and Findings…………………………………………………………………………. 12
Application and Benefits……………………………………………………………………………………… 12
Implications……………………………………………………………………………………………………….. 12
Recommendations for Policy……………………………………………………………………………… 12
Recommendations for Practice…………………………………………………………………………… 12
Recommendations for Future Work…………………………………………………………………….. 12
Conclusion…………………………………………………………………………………………………………. 12
REFERENCES………………………………………………………………………………………………….. 13
APPENDIX A. TITLE OF APPENDIX A……………………………………………………………. 14
APPENDIX B. TITLE OF APPENDIX B……………………………………………………………. 15
List of Tables
Table 1. Set Table and Figure Titles in Title Case………………………………………………………… xx
Table 2.. Title ………………………………………………………………………………………………………….. xx
List of Figures
Figure 1. Set Table and Figure Titles in Title Case………………………………………………………… xx
Figure 2. Title ………………………………………………………………………………………………………….. xx
SECTION 1. PROJECT DESCRIPTION
Overview of the Project
The digital era has been accompanied by a new era of previously unseen convenience of financial transactions, but has also contributed to the increased scale of financial fraud in the United States. The financial industry is constantly combating more and more complex fraud cases, including credit card fraud and identity theft, wire transfer fraud, and account hijackings (Afjal et al., 2023).
Moreover, in the third quarter of 2024 alone, American consumers reported about 58 million worth of credit card fraud, the least reported figure of the year (Statista, 2025). The number underscores the urgency to have smarter and more responsive fraud detection systems that can identify and thwart unlawful practices in real time.
Current fraud detection strategies are mostly human-based or pre-coded rules, which may not respond to arising fraud in financial institutions. Emerging technologies, in particular, the application of artificial intelligence (AI) and machine learning (ML) algorithms, offer the prospects of developing more sophisticated and responsive algorithmic-based fraud detection methods (Pattnaik et al., 2024).
There are financial institutions that are not utilizing AI technologies in detecting fraud fully. Fraud schemes are growing more advanced, which means that organizational leaders, instead of technological resolutions, should pursue a management-based innovation strategy (McKinsey and Company, 2022). In spite of technological improvements, organizational resistance, lack of leadership, and the absence of cross-functional alignment, it is common to witness the underutilization of fraud detection tools. The problems underscore a practice vacuum in that there is a high number of general managers who do not have a roadmap on how to incorporate AI strategic and operational frameworks in institutions.
Banks and fintech businesses are especially susceptible to fraud in the U.S. because of the extent and frequency of online transactions (Brogi and Lagasio, 2024). The rapidity of payment systems in real-time reduces the time that allows intercepting fraud (Vanini et al., 2023). There is high pressure on institutions to use a powerful fraud detection system that is capable of detecting abnormalities, raising red flags, and automatically responding in milliseconds.
Abikoye et al. (2024) established that fraud cases among financial institutions are significantly decreased by aligning the power of the ML with the strategic goals of the organization. Bevilacqua et al. (2025) emphasized the role of managerial ability and organizational readiness in the delivery of the business value of ML initiatives. The vital role of organizational efforts is to make the fraud detection initiatives successful in the long-term and reduce risk exposure.
The project goal is to use ML algorithms in reducing the frauds within American financial organizations. The anomaly detection capabilities of ML are in favor of the leaders to use an effective fraud prevention system to stop fraudulent operations (Dama et al., 2024). The lack of leadership strategies to implement the ML technology to fight fraud activities in financial institutions can be considered the identified root problem (Gupta et al., 2025).
The issue under consideration is that the management within financial institutions does not usually have the strategic thinking and operational models to integrate superior technologies like ML to address the problem of financial fraud appropriately (Chenguel, 2020). A practical disconnect in such situations is the ability of managers to infuse the solutions into organizational practices and decision-making systems, provided technological solutions are available. The importance of the project is to offer significant returns to financial companies and to make the financial system more secure for the consumer by actively detecting and deterring fraudulent dealings.
The importance of this project can be of value to the heads of financial institutions to minimize financial losses through the ability to detect fraud faster and more precisely. The adoption of effective leadership strategies makes the implementation of ML technology possible, which consists of the reduction of the incidents of fraud by means of active detection (Bevilacqua et al., 2025).
In such a way, the culture of innovation with the help of the use of ML would contribute to addressing the arising fraud risks and increasing the financial stability of the organization. Thus, the project aims at addressing a business challenge within the general management field: the implementation and management of smart fraud detection systems is ineffective (Chenguel, 2020). Given that those aspects of the integration of the ML technology relate to the managerial aspect, the data provided in this project may present a pathway through which the financial institutions that consider adopting the measures to prevent fraud can be able to ensure long term security and trust in the digital world.
Problem Statement and Purpose
The problematic business situation is a reduction in profitability and the level of customer satisfaction in the case of fraud (Feingold & Wood, 2024). The conventional fraud detection systems cannot detect fraud and affect the performance of the organization.
Federal Trade Commission (FTC) states that the consumers in the United States had claims totaling up to $90 -501 million loss through defrauds (FTC, 2025). The accumulating losses suggest that not only is the problem of fraud not vanishing, but it is becoming more and more sophisticated and is one of the most dangerous threats to consumer confidence and the stability of the organization.
The targeted business issue is that the U.S. financial sector has several technology managers lacking the resources and technology strategies to install ML fraud protection (Lamey et al., 2024). Nevertheless, the technologies are available to financial institutions, yet poor leadership and strategic incompetence will lead to unsuccessful applications of fraud detection systems, which will hurt the performance of the institution.
It has been found that the lack of leadership among adopting advanced technology is a severe inhibitor, and about 2.6 million consumers have stated that they were victims of fraud because of the mismatched strategies (FTC, 2025). The issue has a number of negative consequences, such as the long-term presence of vulnerability to fraud, the loss of consumer trust, and serious losses (Afjal et al., 2023). The lack of correspondence between the technological capability and the strategy management is a critical area of concern in the bigger picture of the general management field in the financial sector.
Alignment with Program
The project about utilizing the ML technology via strategic leadership in financial institutions will be a great fit in a Doctorate of Business Administration (DBA) program, given the fact that the project concerns a high-impact business issue in the finance sector. Financial fraud is also among the most expensive and complex issues in the banking and financial services industry. In this way, the project has the research problem of the contribution of the strategic management weaknesses to the failure in the adoption of the ML, which results in financial loss, regulatory risk, and reputational damage.
The problem disclosed the relevance of the way the leadership could assist in enhancing financial activities by incorporating ML technology (Pattnaik et al., 2024). In such a way, the project is ideal in the context of the DBA’s focus on interdisciplinary leadership and strategic management. The ability of the financial leaders to explain the decisions necessary to implement advanced technology offers a good understanding of the enhancement of the operations on a financial basis in an organization, and mitigating fraud. The DBA project is concerned with the solution of intricate business issues by conducting applied research.
Purpose Statement
This generic qualitative inquiry project is aimed at understanding the views of managers working in the U.S. financial sector who have been accustomed to adopting resource and technology strategies to execute the ML fraud detection and protection. The project will dwell on the principles of the leadership strategy to consider the use of ML technology in the detection of fraud (Dama et al., 2024). The target population will include the U.S. financial leaders and executives in institutions dealing in the banking and financial services sector in the United States.
Gap in Practice
The gap in practice is that some U.S. financial leaders have failed to establish effective strategies to minimize fraud detection in financial institutions (Chenguel, 2020). The use of standard systems in detecting fraud is failing to keep pace with the evolving practices of fraudsters, and it is likely to generate fraudulent acts. The practice gap does not exist based on the inaccessibility of fraud detection technologies but rather the absence of a leadership strategic approach to introduce the ML technology (Hariyani et al., 2024). The difference also converts into the specific problem that financial institutions are vulnerable to sophisticated fraudulent schemes that cannot be detected by the existing systems, leading to the loss of money.
An optimal situation would be one in which leaders of financial institutions are active in employing the predictive power of ML to curb and prevent real-time fraud with high-precision (Pattnaik et al., 2024). The results of the project are potentially useful to practitioners who may wish to bridge the gap by demonstrating the possible worth of adopting more analytical approaches to the prevention of fraud. Also, the outcomes should be considered within the framework of a strategic plan of a company.
Theoretical Framework
Project Context
Historical Background and Current Trends
Synthesis of the Scholarly Literature
Synthesis of the Practitioner Literature
Alignment of the Project With the Literature and Discipline
SECTION 2. PROCESS
Project Questions
Project Design/Method
Stakeholders, Participants, and Target Audience
Role of the Researcher
Project Study Protocol
Sample
Data Collection
Ethical Considerations
Data Analysis
Figure 1
Types of Garbage
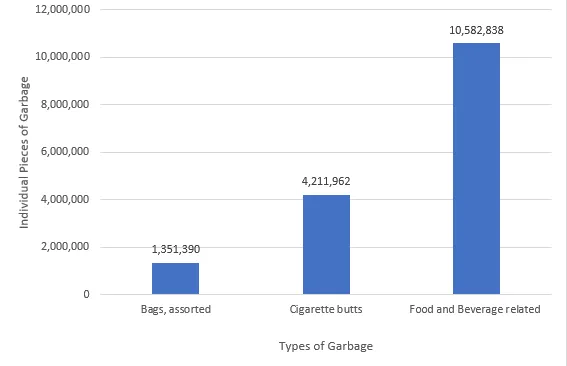
Note: Insert information about the source or presentation of the data if you did not create the figure. Add copyright/permission notes for copied information, even government materials, which require a 10-point acknowledgment below the image. Be sure to include a permission acknowledgment, e.g., “Reprinted [or adapted] with permission.” See the templates at https://academicwriter-apa-org.library.capella.edu/learn/browse/QG-28.
Table 1
Demographic Information
Participant | Age | Sex | Position | Years in position |
P1 | 25-30 | Male | Chairman | 10-15 |
P2 | 41-45 | Female | CEO | 6-10 |
Note. Potential participants under age 16 were omitted from the sample. Only essential notes need to be included. See Table setup (apa.org) and https://academicwriter-apa-org.library.capella.edu/learn/browse/QG-44?group=All&view=list&term=tables&sort=asc. The Doctoral Publications Guidebook also addresses tables and figures.
SECTION 3. FINDINGS AND APPLICATION
Relevant Outcomes and Findings
Application and Benefits
Implications
Recommendations for Policy
Recommendations for Practice
Recommendations for Future Work
Conclusion
………………………………
Related Free Assessment for DB-FPX8840
Instructions to write
DB FPX 8840 Assessment 2
References for
DB FPX 8840 Assessment 2
Abikoye, N. B. E., Akinwunmi, N. T., Adelaja, N. A. O., Chidozie, S., & Ogunsuji, M. (2024).
Real-time financial monitoring systems:
Enhancing risk management through continuous oversight.
GSC Advanced Research and Reviews, 20(1), 465-476.
https://doi.org/10.30574/gscarr.2024.20.1.0287
Afjal, M., Salamzadeh, A., & Dana, L. P. (2023). Financial fraud and credit risk:
Illicit practices and their impact on banking stability.
Journal of Risk and Financial Management, 16(9), 386.
https://doi.org/10.3390/jrfm16090386
Bevilacqua, S., Masárová, J., Perotti, F. A., & Ferraris, A. (2025).
Enhancing top managers’ leadership with artificial intelligence:
Insights from a systematic literature review. Review of Managerial Science.
https://doi.org/10.1007/s11846-025-00836-7
Brogi, M., & Lagasio, V. (2024). New but naughty. The evolution of misconduct in FinTech.
International Review of Financial Analysis, 95, e103489.
https://doi.org/10.1016/j.irfa.2024.103489
Chenguel, M. (2020). Financial fraud and managers’ causes and effects. Corporate Social Responsibility.
https://doi.org/10.5772/intechopen.93494
Dama, K., Reddy, K., Hrithik, K., Raheem, D., & Vyshnavi. (2024). Fraud detection in financial transactions. Researchgate.net.
https://www.researchgate.net/publication/379654286_Fraud_Detection_in_Financial_Transactions
Federal Trade Commission. (2025). New FTC data show a big jump in reported losses to fraud to $12.5 billion in 2024. Ftc.gov.
Feingold, S., & Wood, J. (2024, April 10). “Pig-butchering” scams on the rise as technology amplifies financial fraud, INTERPOL warns. Weforum.org.
https://www.weforum.org/stories/2024/04/interpol-financial-fraud-scams-cybercrime/
Gupta, R. K., Hassan, A., Majhi, S. K., Parveen, N., Zamani, A. T., Anitha, R., Ojha, B., Singh, A. K., & Muduli, D. (2025).
Enhanced framework for credit card fraud detection using robust feature selection and a stacking ensemble model approach.
Results in Engineering, 26, e105084.
https://doi.org/10.1016/j.rineng.2025.105084
Hariyani, D., Hariyani, P., Mishra, S., & Sharma, M. K. (2024). Causes of organizational failure: A literature review.
Social Sciences & Humanities Open, 10, e101153. https://doi.org/10.1016/j.ssaho.2024.101153
Lamey, Y. M., Tawfik, O. I., Durrah, O., & Elmaasrawy, H. E. (2024). Fintech adoption and banks’ non-financial performance:
Do circular economy practices matter? Journal of Risk and Financial Management, 17(8), 319.
https://doi.org/10.3390/jrfm17080319
McKinsey & Company. (2022). Four key capabilities to strengthen a fraud management system | McKinsey. Mckinsey.com.
Pattnaik, D., Ray, S., & Raman, R. (2024). Applications of artificial intelligence and machine learning in the financial services industry:
A bibliometric review. Heliyon, 10(1), e23492.
https://www.sciencedirect.com/science/article/pii/S2405844023107006
Statista. (2025). Value of fraud loss in the U.S. by payment method 2021. Statista.com.
https://www.statista.com/statistics/958997/fraud-loss-usa-by-payment-method/
Vanini, P., Rossi, S., Zvizdic, E., & Domenig, T. (2023). Online payment fraud: from anomaly detection to risk management. Financial Innovation, 9(1).
https://doi.org/10.1186/s40854-023-00470-w
APPENDIX A. TITLE OF APPENDIX A
Format titles as shown here. Do not include recruitment flyers, permissions correspondence, invitations to subject matter experts, or informed consent forms. They should be removed before submission to the committee and doctoral publications review. Place tables and figures in the sections at the point where they are discussed.
APPENDIX B. TITLE OF APPENDIX B
Format titles as shown here. Do not include recruitment flyers, permissions correspondence, invitations to subject matter experts, or informed consent forms. They should be removed before submission to the committee and doctoral publications review. Place tables and figures in the sections at the point where they are discussed.
Capella Professor to choose for
DB FPX 8840 Assessment 2
- Bradly E. Roh.
- Maja Zelihic.
- Kevin Knight.
- Melvia Scott.
- Pamela Meares.
(FAQ's) related to
DB FPX 8840 Assessment 2
Question 1: From where to download a free sample for DB FPX 8840 Assessment 2?
Answer 1: Download a free sample for DB FPX 8840 Assessment 2 from DB FPX.
Do you need a tutor to help with this paper for you with in 24 hours
- 0% Plagiarised
- 0% AI
- Distinguish grades guarantee
- 24 hour delivery